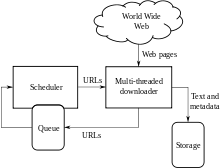
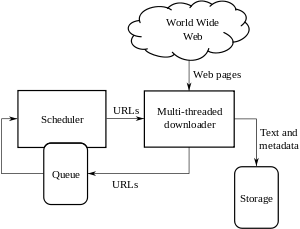
Architecture of a Web crawler
A Web crawler, sometimes called a spider or spiderbot and often shortened to crawler, is an Internet bot that systematically browses the World Wide Web, typically for the purpose of Web indexing (web spidering).
Web search engines and some other sites use Web crawling or spidering software to update their web content or indices of others sites' web content. Web crawlers copy pages for processing by a search engine which indexes the downloaded pages so users can search more efficiently.
Crawlers consume resources on visited systems and often visit
sites without approval. Issues of schedule, load, and "politeness" come
into play when large collections of pages are accessed. Mechanisms exist
for public sites not wishing to be crawled to make this known to the
crawling agent. For example, including a robots.txt file can request bots to index only parts of a website, or nothing at all.
The number of Internet pages is extremely large; even the largest
crawlers fall short of making a complete index. For this reason, search
engines struggled to give relevant search results in the early years of
the World Wide Web, before 2000. Today, relevant results are given
almost instantly.
Nomenclature
A web crawler is also known as a spider, an ant, an automatic indexer, or (in the FOAF software context) a Web scutter.
Overview
A Web crawler starts with a list of URLs to visit, called the seeds. As the crawler visits these URLs, it identifies all the hyperlinks in the pages and adds them to the list of URLs to visit, called the crawl frontier. URLs from the frontier are recursively visited according to a set of policies. If the crawler is performing archiving of websites
it copies and saves the information as it goes. The archives are
usually stored in such a way they can be viewed, read and navigated as
they were on the live web, but are preserved as ‘snapshots'.
The archive is known as the repository and is designed to store and manage the collection of web pages. The repository only stores HTML
pages and these pages are stored as distinct files. A repository is
similar to any other system that stores data, like a modern day
database. The only difference is that a repository does not need all the
functionality offered by a database system. The repository stores the
most recent version of the web page retrieved by the crawler.
The large volume implies the crawler can only download a limited
number of the Web pages within a given time, so it needs to prioritize
its downloads. The high rate of change can imply the pages might have
already been updated or even deleted.
The number of possible URLs crawled being generated by
server-side software has also made it difficult for web crawlers to
avoid retrieving duplicate content. Endless combinations of HTTP GET
(URL-based) parameters exist, of which only a small selection will
actually return unique content. For example, a simple online photo
gallery may offer three options to users, as specified through HTTP GET parameters in the URL. If there exist four ways to sort images, three choices of thumbnail
size, two file formats, and an option to disable user-provided content,
then the same set of content can be accessed with 48 different URLs,
all of which may be linked on the site. This mathematical combination
creates a problem for crawlers, as they must sort through endless
combinations of relatively minor scripted changes in order to retrieve
unique content.
As Edwards et al. noted, "Given that the bandwidth
for conducting crawls is neither infinite nor free, it is becoming
essential to crawl the Web in not only a scalable, but efficient way, if
some reasonable measure of quality or freshness is to be maintained." A crawler must carefully choose at each step which pages to visit next.
Crawling policy
The behavior of a Web crawler is the outcome of a combination of policies:
- a selection policy which states the pages to download,
- a re-visit policy which states when to check for changes to the pages,
- a politeness policy that states how to avoid overloading Web sites.
- a parallelization policy that states how to coordinate distributed web crawlers.
Selection policy
Given
the current size of the Web, even large search engines cover only a
portion of the publicly available part. A 2009 study showed even
large-scale search engines index no more than 40-70% of the indexable Web; a previous study by Steve Lawrence and Lee Giles showed that no search engine indexed more than 16% of the Web in 1999. As a crawler always downloads just a fraction of the Web pages, it is highly desirable for the downloaded fraction to contain the most relevant pages and not just a random sample of the Web.
This requires a metric of importance for prioritizing Web pages. The importance of a page is a function of its intrinsic quality, its popularity in terms of links or visits, and even of its URL (the latter is the case of vertical search engines restricted to a single top-level domain,
or search engines restricted to a fixed Web site). Designing a good
selection policy has an added difficulty: it must work with partial
information, as the complete set of Web pages is not known during
crawling.
Junghoo Cho et al. made the first study on policies for crawling scheduling. Their data set was a 180,000-pages crawl from the stanford.edu domain, in which a crawling simulation was done with different strategies. The ordering metrics tested were breadth-first, backlink count and partial PageRank
calculations. One of the conclusions was that if the crawler wants to
download pages with high Pagerank early during the crawling process,
then the partial Pagerank strategy is the better, followed by
breadth-first and backlink-count. However, these results are for just a
single domain. Cho also wrote his Ph.D. dissertation at Stanford on web
crawling.
Najork and Wiener performed an actual crawl on 328 million pages, using breadth-first ordering.
They found that a breadth-first crawl captures pages with high Pagerank
early in the crawl (but they did not compare this strategy against
other strategies). The explanation given by the authors for this result
is that "the most important pages have many links to them from numerous
hosts, and those links will be found early, regardless of on which host
or page the crawl originates."
Abiteboul designed a crawling strategy based on an algorithm called OPIC (On-line Page Importance Computation).
In OPIC, each page is given an initial sum of "cash" that is
distributed equally among the pages it points to. It is similar to a
PageRank computation, but it is faster and is only done in one step. An
OPIC-driven crawler downloads first the pages in the crawling frontier
with higher amounts of "cash". Experiments were carried in a
100,000-pages synthetic graph with a power-law distribution of in-links.
However, there was no comparison with other strategies nor experiments
in the real Web.
Boldi et al. used simulation on subsets of the Web of 40 million pages from the .it
domain and 100 million pages from the WebBase crawl, testing
breadth-first against depth-first, random ordering and an omniscient
strategy. The comparison was based on how well PageRank computed on a
partial crawl approximates the true PageRank value. Surprisingly, some
visits that accumulate PageRank very quickly (most notably,
breadth-first and the omniscient visit) provide very poor progressive
approximations.
Baeza-Yates et al. used simulation on two subsets of the Web of 3 million pages from the .gr and .cl domain, testing several crawling strategies. They showed that both the OPIC strategy and a strategy that uses the length of the per-site queues are better than breadth-first crawling, and that it is also very effective to use a previous crawl, when it is available, to guide the current one.
Daneshpajouh et al. designed a community based algorithm for discovering good seeds.
Their method crawls web pages with high PageRank from different
communities in less iteration in comparison with crawl starting from
random seeds. One can extract good seed from a previously-crawled-Web
graph using this new method. Using these seeds, a new crawl can be very
effective.
Restricting followed links
A crawler may only want to seek out HTML pages and avoid all other MIME types.
In order to request only HTML resources, a crawler may make an HTTP
HEAD request to determine a Web resource's MIME type before requesting
the entire resource with a GET request. To avoid making numerous HEAD
requests, a crawler may examine the URL and only request a resource if
the URL ends with certain characters such as .html, .htm, .asp, .aspx,
.php, .jsp, .jspx or a slash. This strategy may cause numerous HTML Web
resources to be unintentionally skipped.
Some crawlers may also avoid requesting any resources that have a "?" in them (are dynamically produced) in order to avoid spider traps
that may cause the crawler to download an infinite number of URLs from a
Web site. This strategy is unreliable if the site uses URL rewriting to simplify its URLs.
URL normalization
Crawlers usually perform some type of URL normalization in order to avoid crawling the same resource more than once. The term URL normalization, also called URL canonicalization,
refers to the process of modifying and standardizing a URL in a
consistent manner. There are several types of normalization that may be
performed including conversion of URLs to lowercase, removal of "." and
".." segments, and adding trailing slashes to the non-empty path
component.
Path-ascending crawling
Some crawlers intend to download/upload as many resources as possible from a particular web site. So path-ascending crawler was introduced that would ascend to every path in each URL that it intends to crawl.
For example, when given a seed URL of
http://llama.org/hamster/monkey/page.html, it will attempt to crawl
/hamster/monkey/, /hamster/, and /. Cothey found that a path-ascending
crawler was very effective in finding isolated resources, or resources
for which no inbound link would have been found in regular crawling.
Focused crawling
The importance of a page for a crawler can also be expressed as a
function of the similarity of a page to a given query. Web crawlers that
attempt to download pages that are similar to each other are called focused crawler or topical crawlers. The concepts of topical and focused crawling were first introduced by Filippo Menczer and by Soumen Chakrabarti et al.
The main problem in focused crawling is that in the context of a
Web crawler, we would like to be able to predict the similarity of the
text of a given page to the query before actually downloading the page. A
possible predictor is the anchor text of links; this was the approach
taken by Pinkerton in the first web crawler of the early days of the Web. Diligenti et al.
propose using the complete content of the pages already visited to
infer the similarity between the driving query and the pages that have
not been visited yet. The performance of a focused crawling depends
mostly on the richness of links in the specific topic being searched,
and a focused crawling usually relies on a general Web search engine for
providing starting points.
Academic-focused crawler
An example of the focused crawlers are academic crawlers, which crawls free-access academic related documents, such as the citeseerxbot, which is the crawler of CiteSeerX search engine. Other academic search engines are Google Scholar and Microsoft Academic Search etc. Because most academic papers are published in PDF formats, such kind of crawler is particularly interested in crawling PDF, PostScript files, Microsoft Word including their zipped formats. Because of this, general open source crawlers, such as Heritrix, must be customized to filter out other MIME types, or a middleware is used to extract these documents out and import them to the focused crawl database and repository.
Identifying whether these documents are academic or not is challenging
and can add a significant overhead to the crawling process, so this is
performed as a post crawling process using machine learning or regular expression
algorithms. These academic documents are usually obtained from home
pages of faculties and students or from publication page of research
institutes. Because academic documents takes only a small fraction in
the entire web pages, a good seed selection are important in boosting
the efficiencies of these web crawlers. Other academic crawlers may download plain text and HTML files, that contains metadata
of academic papers, such as titles, papers, and abstracts. This
increases the overall number of papers, but a significant fraction may
not provide free PDF downloads.
Semantic focused crawler
Another type of focused crawlers is semantic focused crawler, which makes use of domain ontologies to represent topical maps and link Web pages with relevant ontological concepts for the selection and categorization purposes. In addition, ontologies can be automatically updated in the crawling process. Dong et al.
introduced such an ontology-learning-based crawler using support vector
machine to update the content of ontological concepts when crawling Web
Pages.
Re-visit policy
The
Web has a very dynamic nature, and crawling a fraction of the Web can
take weeks or months. By the time a Web crawler has finished its crawl,
many events could have happened, including creations, updates, and
deletions.
From the search engine's point of view, there is a cost
associated with not detecting an event, and thus having an outdated copy
of a resource. The most-used cost functions are freshness and age.
Freshness: This is a binary measure that indicates whether the local copy is accurate or not. The freshness of a page p in the repository at time t is defined as:
Age: This is a measure that indicates how outdated the local copy is. The age of a page p in the repository, at time t is defined as:
Coffman et al.
worked with a definition of the objective of a Web crawler that is
equivalent to freshness, but use a different wording: they propose that a
crawler must minimize the fraction of time pages remain outdated. They
also noted that the problem of Web crawling can be modeled as a
multiple-queue, single-server polling system, on which the Web crawler
is the server and the Web sites are the queues. Page modifications are
the arrival of the customers, and switch-over times are the interval
between page accesses to a single Web site. Under this model, mean
waiting time for a customer in the polling system is equivalent to the
average age for the Web crawler.
The objective of the crawler is to keep the average freshness of
pages in its collection as high as possible, or to keep the average age
of pages as low as possible. These objectives are not equivalent: in the
first case, the crawler is just concerned with how many pages are
out-dated, while in the second case, the crawler is concerned with how
old the local copies of pages are.
Evolution of Freshness and Age in a web crawler
Two simple re-visiting policies were studied by Cho and Garcia-Molina:
- Uniform policy: This involves re-visiting all pages in the collection with the same frequency, regardless of their rates of change.
- Proportional policy: This involves re-visiting more often the pages that change more frequently. The visiting frequency is directly proportional to the (estimated) change frequency.
In both cases, the repeated crawling order of pages can be done either in a random or a fixed order.
Cho and Garcia-Molina proved the surprising result that, in terms
of average freshness, the uniform policy outperforms the proportional
policy in both a simulated Web and a real Web crawl. Intuitively, the
reasoning is that, as web crawlers have a limit to how many pages they
can crawl in a given time frame, (1) they will allocate too many new
crawls to rapidly changing pages at the expense of less frequently
updating pages, and (2) the freshness of rapidly changing pages lasts
for shorter period than that of less frequently changing pages. In other
words, a proportional policy allocates more resources to crawling
frequently updating pages, but experiences less overall freshness time
from them.
To improve freshness, the crawler should penalize the elements that change too often.
The optimal re-visiting policy is neither the uniform policy nor the
proportional policy. The optimal method for keeping average freshness
high includes ignoring the pages that change too often, and the optimal
for keeping average age low is to use access frequencies that
monotonically (and sub-linearly) increase with the rate of change of
each page. In both cases, the optimal is closer to the uniform policy
than to the proportional policy: as Coffman et al.
note, "in order to minimize the expected obsolescence time, the
accesses to any particular page should be kept as evenly spaced as
possible".
Explicit formulas for the re-visit policy are not attainable in
general, but they are obtained numerically, as they depend on the
distribution of page changes. Cho and Garcia-Molina show that the
exponential distribution is a good fit for describing page changes, while Ipeirotis et al. show how to use statistical tools to discover parameters that affect this distribution.
Note that the re-visiting policies considered here regard all pages as
homogeneous in terms of quality ("all pages on the Web are worth the
same"), something that is not a realistic scenario, so further
information about the Web page quality should be included to achieve a
better crawling policy.
Politeness policy
Crawlers
can retrieve data much quicker and in greater depth than human
searchers, so they can have a crippling impact on the performance of a
site. Needless to say, if a single crawler is performing multiple
requests per second and/or downloading large files, a server would have a
hard time keeping up with requests from multiple crawlers.
As noted by Koster, the use of Web crawlers is useful for a number of tasks, but comes with a price for the general community. The costs of using Web crawlers include:
- network resources, as crawlers require considerable bandwidth and operate with a high degree of parallelism during a long period of time;
- server overload, especially if the frequency of accesses to a given server is too high;
- poorly written crawlers, which can crash servers or routers, or which download pages they cannot handle; and
- personal crawlers that, if deployed by too many users, can disrupt networks and Web servers.
A partial solution to these problems is the robots exclusion protocol,
also known as the robots.txt protocol that is a standard for
administrators to indicate which parts of their Web servers should not
be accessed by crawlers.
This standard does not include a suggestion for the interval of visits
to the same server, even though this interval is the most effective way
of avoiding server overload. Recently commercial search engines like Google, Ask Jeeves, MSN and Yahoo! Search are able to use an extra "Crawl-delay:" parameter in the robots.txt file to indicate the number of seconds to delay between requests.
The first proposed interval between successive pageloads was 60 seconds.
However, if pages were downloaded at this rate from a website with more
than 100,000 pages over a perfect connection with zero latency and
infinite bandwidth, it would take more than 2 months to download only
that entire Web site; also, only a fraction of the resources from that
Web server would be used. This does not seem acceptable.
Cho uses 10 seconds as an interval for accesses, and the WIRE crawler uses 15 seconds as the default. The MercatorWeb crawler follows an adaptive politeness policy: if it took t seconds to download a document from a given server, the crawler waits for 10t seconds before downloading the next page. Dill et al. use 1 second.
For those using Web crawlers for research purposes, a more
detailed cost-benefit analysis is needed and ethical considerations
should be taken into account when deciding where to crawl and how fast
to crawl.
Anecdotal evidence from access logs shows that access intervals
from known crawlers vary between 20 seconds and 3–4 minutes. It is worth
noticing that even when being very polite, and taking all the
safeguards to avoid overloading Web servers, some complaints from Web
server administrators are received. Brin and Page
note that: "... running a crawler which connects to more than half a
million servers (...) generates a fair amount of e-mail and phone calls.
Because of the vast number of people coming on line, there are always
those who do not know what a crawler is, because this is the first one
they have seen."
Parallelization policy
A parallel
crawler is a crawler that runs multiple processes in parallel. The goal
is to maximize the download rate while minimizing the overhead from
parallelization and to avoid repeated downloads of the same page. To
avoid downloading the same page more than once, the crawling system
requires a policy for assigning the new URLs discovered during the
crawling process, as the same URL can be found by two different crawling
processes.
Architectures
High-level architecture of a standard Web crawler
A crawler must not only have a good crawling strategy, as noted in
the previous sections, but it should also have a highly optimized
architecture.
Shkapenyuk and Suel noted that:
While it is fairly easy to build a slow crawler that downloads a few pages per second for a short period of time, building a high-performance system that can download hundreds of millions of pages over several weeks presents a number of challenges in system design, I/O and network efficiency, and robustness and manageability.
Web crawlers are a central part of search engines, and details on
their algorithms and architecture are kept as business secrets. When
crawler designs are published, there is often an important lack of
detail that prevents others from reproducing the work. There are also
emerging concerns about "search engine spamming", which prevent major search engines from publishing their ranking algorithms.
Security
While most of the website owners are keen to have their pages indexed as broadly as possible to have strong presence in search engines, web crawling can also have unintended consequences and lead to a compromise or data breach
if a search engine indexes resources that shouldn't be publicly
available, or pages revealing potentially vulnerable versions of
software.
Apart from standard web application security
recommendations website owners can reduce their exposure to
opportunistic hacking by only allowing search engines to index the
public parts of their websites (with robots.txt) and explicitly blocking them from indexing transactional parts (login pages, private pages, etc.).
Crawler identification
Web crawlers typically identify themselves to a Web server by using the User-agent field of an HTTP request. Web site administrators typically examine their Web servers'
log and use the user agent field to determine which crawlers have
visited the web server and how often. The user agent field may include a
URL
where the Web site administrator may find out more information about
the crawler. Examining Web server log is tedious task, and therefore
some administrators use tools to identify, track and verify Web
crawlers. Spambots
and other malicious Web crawlers are unlikely to place identifying
information in the user agent field, or they may mask their identity as a
browser or other well-known crawler.
It is important for Web crawlers to identify themselves so that
Web site administrators can contact the owner if needed. In some cases,
crawlers may be accidentally trapped in a crawler trap
or they may be overloading a Web server with requests, and the owner
needs to stop the crawler. Identification is also useful for
administrators that are interested in knowing when they may expect their
Web pages to be indexed by a particular search engine.
Crawling the deep web
A vast amount of web pages lie in the deep or invisible web.
These pages are typically only accessible by submitting queries to a
database, and regular crawlers are unable to find these pages if there
are no links that point to them. Google's Sitemaps protocol and mod oai are intended to allow discovery of these deep-Web resources.
Deep web crawling also multiplies the number of web links to be crawled. Some crawlers only take some of the URLs in
Strategic approaches may be taken to target deep Web content. With a technique called screen scraping,
specialized software may be customized to automatically and repeatedly
query a given Web form with the intention of aggregating the resulting
data. Such software can be used to span multiple Web forms across
multiple Websites. Data extracted from the results of one Web form
submission can be taken and applied as input to another Web form thus
establishing continuity across the Deep Web in a way not possible with
traditional web crawlers.
Pages built on AJAX
are among those causing problems to web crawlers. Google has proposed a
format of AJAX calls that their bot can recognize and index.
Web crawler bias
A
recent study based on a large scale analysis of robots.txt files showed
that certain web crawlers were preferred over others, with Googlebot
being the most preferred web crawler.
Visual vs programmatic crawlers
There
are a number of "visual web scraper/crawler" products available on the
web which will crawl pages and structure data into columns and rows
based on the users requirements. One of the main difference between a
classic and a visual crawler is the level of programming ability
required to set up a crawler. The latest generation of "visual scrapers"
like Diffbot, outwithub, and import.io remove the majority of the programming skill needed to be able to program and start a crawl to scrape web data.
The visual scraping/crawling method relies on the user "teaching"
a piece of crawler technology, which then follows patterns in
semi-structured data sources. The dominant method for teaching a visual
crawler is by highlighting data in a browser and training columns and
rows. While the technology is not new, for example it was the basis of
Needlebase which has been bought by Google (as part of a larger
acquisition of ITA Labs), there is continued growth and investment in this area by investors and end-users.
Examples
The following is a list of published crawler architectures for
general-purpose crawlers (excluding focused web crawlers), with a brief
description that includes the names given to the different components
and outstanding features:
- Bingbot is the name of Microsoft's Bing webcrawler. It replaced Msnbot.
- Googlebot is described in some detail, but the reference is only about an early version of its architecture, which was based in C++ and Python. The crawler was integrated with the indexing process, because text parsing was done for full-text indexing and also for URL extraction. There is a URL server that sends lists of URLs to be fetched by several crawling processes. During parsing, the URLs found were passed to a URL server that checked if the URL have been previously seen. If not, the URL was added to the queue of the URL server.
- SortSite
- Swiftbot is Swiftype's web crawler.
- WebCrawler was used to build the first publicly available full-text index of a subset of the Web. It was based on lib-WWW to download pages, and another program to parse and order URLs for breadth-first exploration of the Web graph. It also included a real-time crawler that followed links based on the similarity of the anchor text with the provided query.
- WebFountain is a distributed, modular crawler similar to Mercator but written in C++.
- World Wide Web Worm was a crawler used to build a simple index of document titles and URLs. The index could be searched by using the grep Unix command.
- Xenon is a web crawler used by government tax authorities to detect fraud.
- Yahoo! Slurp was the name of the Yahoo! Search crawler until Yahoo! contracted with Microsoft to use Bingbot instead.
Open-source crawlers
- Frontera is web crawling framework implementing crawl frontier component and providing scalability primitives for web crawler applications.
- GNU Wget is a command-line-operated crawler written in C and released under the GPL. It is typically used to mirror Web and FTP sites.
- GRUB is an open source distributed search crawler that Wikia Search used to crawl the web.
- Heritrix is the Internet Archive's archival-quality crawler, designed for archiving periodic snapshots of a large portion of the Web. It was written in Java.
- ht://Dig includes a Web crawler in its indexing engine.
- HTTrack uses a Web crawler to create a mirror of a web site for off-line viewing. It is written in C and released under the GPL.
- mnoGoSearch is a crawler, indexer and a search engine written in C and licensed under the GPL (*NIX machines only)
- Norconex HTTP Collector is a web spider, or crawler, written in Java, that aims to make Enterprise Search integrators and developers's life easier (licensed under Apache License).
- Apache Nutch is a highly extensible and scalable web crawler written in Java and released under an Apache License. It is based on Apache Hadoop and can be used with Apache Solr or Elasticsearch.
- Open Search Server is a search engine and web crawler software release under the GPL.
- PHP-Crawler is a simple PHP and MySQL based crawler released under the BSD License.
- Scrapy, an open source webcrawler framework, written in python (licensed under BSD).
- Seeks, a free distributed search engine (licensed under AGPL).
- StormCrawler, a collection of resources for building low-latency, scalable web crawlers on Apache Storm (Apache License).
- tkWWW Robot, a crawler based on the tkWWW web browser (licensed under GPL).
- Xapian, a search crawler engine, written in c++.
- YaCy, a free distributed search engine, built on principles of peer-to-peer networks (licensed under GPL).
- Trandoshan, a free, open source distributed web-crawler designed for the deep-web.