From Wikipedia, the free encyclopedia
https://en.wikipedia.org/wiki/Central_Intelligence_Agency
 Seal of the Central Intelligence Agency | |
 Flag of the Central Intelligence Agency | |
 CIA headquarters, Langley, Virginia | |
| Agency overview | |
|---|---|
| Formed | September 18, 1947 |
| Preceding agency | |
| Type | Independent (component of the Intelligence Community) |
| Headquarters | George Bush Center for Intelligence Langley, Virginia, U.S. 38°57′07″N 77°08′46″W |
| Motto | "The Work of a Nation. The Center of Intelligence." Unofficial motto: "And ye shall know the truth and the truth shall make you free." (John 8:32) |
| Employees | 21,575 (estimate) |
| Annual budget | $15 billion (as of 2013) |
| Agency executives |
|
| Website | www |
The Central Intelligence Agency (CIA; /siaɪˈeɪ/) is a civilian foreign intelligence service of the federal government of the United States, officially tasked with gathering, processing, and analyzing national security information from around the world, primarily through the use of human intelligence (HUMINT). As a principal member of the United States Intelligence Community (IC), the CIA reports to the Director of National Intelligence and is primarily focused on providing intelligence for the President and Cabinet of the United States.
Unlike the Federal Bureau of Investigation (FBI), which is a domestic security service, the CIA has no law enforcement function and is officially mainly focused on overseas intelligence gathering, with only limited domestic intelligence collection. The CIA serves as the national manager for coordination of HUMINT activities across the U.S. intelligence community. It is the only agency authorized by law to carry out and oversee covert action at the behest of the President. It exerts foreign political influence through its tactical divisions, such as the Special Activities Center. The CIA was also instrumental in establishing intelligence services in several U.S. allied countries, such as Germany's BND. It has also provided support to many foreign political groups and governments, including planning, coordinating, training on torture, technical support, and was involved in several regime changes, terrorist attacks and planned assassinations of foreign leaders.
Since 2004 the CIA is organized under the Director of National Intelligence (DNI). Despite transferring some of its powers to the DNI, the CIA has grown in size as a result of the September 11 attacks. In 2013, The Washington Post reported that in the fiscal year 2010, the CIA had the largest budget of all IC agencies, exceeding previous estimates.
The CIA has increasingly expanded its role, including covert paramilitary operations. One of its largest divisions, the Information Operations Center (IOC), has officially shifted focus from counter-terrorism to offensive cyber-operations.
The agency has been the subject of many controversies, including human rights violations, domestic wiretapping and propaganda, and allegations of drug trafficking. It has also appeared in works of fiction, including books, films and video games.
Purpose
When the CIA was created, its purpose was to create a clearinghouse for foreign policy intelligence and analysis. Today its primary purpose is to collect, analyze, evaluate, and disseminate foreign intelligence, and to perform covert actions.
According to its fiscal 2013 budget, the CIA has five priorities:
- Counterterrorism, the top priority
- Nonproliferation of nuclear and other weapons of mass destruction.
- Warning/informing American leaders of important overseas events.
- Counterintelligence
- Cyber intelligence.
Organizational structure
The CIA has an executive office and five major directorates:
- The Directorate of Digital Innovation
- The Directorate of Analysis
- The Directorate of Operations
- The Directorate of Support
- The Directorate of Science and Technology
Executive Office
The Director of the Central Intelligence Agency (D/CIA) is appointed by the President with Senate confirmation and reports directly to the Director of National Intelligence (DNI); in practice, the CIA director interfaces with the Director of National Intelligence (DNI), Congress, and the White House, while the Deputy Director (DD/CIA) is the internal executive of the CIA and the Chief Operating Officer (COO/CIA), known as Executive Director until 2017, leads the day-to-day work as the third highest post of the CIA. The Deputy Director is formally appointed by the Director without Senate confirmation, but as the President's opinion plays a great role in the decision, the Deputy Director is generally considered a political position, making the Chief Operating Officer the most senior non-political position for CIA career officers.
The Executive Office also supports the U.S. military by providing it with information it gathers, receiving information from military intelligence organizations, and cooperates with field activities. The Executive Director is in charge of the day-to-day operation of the CIA. Each branch of the military service has its own Director. The Associate Director of military affairs, a senior military officer, manages the relationship between the CIA and the Unified Combatant Commands, who produce and deliver to the CIA regional/operational intelligence and consume national intelligence produced by the CIA.
Directorate of Analysis
The Directorate of Analysis, through much of its history known as the Directorate of Intelligence (DI), is tasked with helping "the President and other policymakers make informed decisions about our country's national security" by looking "at all the available information on an issue and organiz[ing] it for policymakers". The Directorate has four regional analytic groups, six groups for transnational issues, and three that focus on policy, collection, and staff support. There is an office dedicated to Iraq; regional analytical offices covering the Near East and South Asia, Russia and Europe; and the Asian Pacific, Latin American, and African offices.
Directorate of Operations
The Directorate of Operations is responsible for collecting foreign intelligence (mainly from clandestine HUMINT sources), and for covert action. The name reflects its role as the coordinator of human intelligence activities between other elements of the wider U.S. intelligence community with their HUMINT operations. This Directorate was created in an attempt to end years of rivalry over influence, philosophy and budget between the United States Department of Defense (DOD) and the CIA. In spite of this, the Department of Defense recently organized its own global clandestine intelligence service, the Defense Clandestine Service (DCS), under the Defense Intelligence Agency (DIA).
This Directorate is known to be organized by geographic regions and issues, but its precise organization is classified.
Directorate of Science and Technology
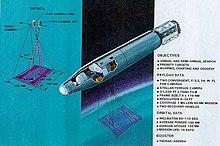
The Directorate of Science & Technology was established to research, create, and manage technical collection disciplines and equipment. Many of its innovations were transferred to other intelligence organizations, or, as they became more overt, to the military services.
For example, the development of the U-2 high-altitude reconnaissance aircraft was done in cooperation with the United States Air Force. The U-2's original mission was clandestine imagery intelligence over denied areas such as the Soviet Union. It was subsequently provided with signals intelligence and measurement and signature intelligence capabilities, and is now operated by the Air Force.
A DS&T organization analyzed imagery intelligence collected by the U-2 and reconnaissance satellites called the National Photointerpretation Center (NPIC), which had analysts from both the CIA and the military services. Subsequently, NPIC was transferred to the National Geospatial-Intelligence Agency (NGA).
Directorate of Support
The Directorate of Support has organizational and administrative functions to significant units including:
- The Office of Security
- The Office of Communications
- The Office of Information Technology
Directorate of Digital Innovation
The Directorate of Digital Innovation (DDI) focuses on accelerating innovation across the Agency's mission activities. It is the Agency's newest directorate. The Langley, Virginia-based office's mission is to streamline and integrate digital and cybersecurity capabilities into the CIA's espionage, counterintelligence, all-source analysis, open-source intelligence collection and covert action operations. It provides operations personnel with tools and techniques to use in cyber operations. It works with information technology infrastructure and practices cyber tradecraft. This means retrofitting the CIA for cyberwarfare. DDI officers help accelerate the integration of innovative methods and tools to enhance the CIA's cyber and digital capabilities on a global scale and ultimately help safeguard the United States. They also apply technical expertise to exploit clandestine and publicly available information (also known as open source data) using specialized methodologies and digital tools to plan, initiate and support the technical and human-based operations of the CIA. Before the establishment of the new digital directorate, offensive cyber operations were undertaken by the CIA's Information Operations Center. Little is known about how the office specifically functions or if it deploys offensive cyber capabilities.
The directorate had been covertly operating since approximately March 2015 but formally began operations on October 1, 2015. According to classified budget documents, the CIA's computer network operations budget for fiscal year 2013 was $685.4 million. The NSA's budget was roughly $1 billion at the time.
Rep. Adam Schiff, the California Democrat who serves as the ranking member of the House Intelligence Committee, endorsed the reorganization. "The director has challenged his workforce, the rest of the intelligence community and the nation to consider how we conduct the business of intelligence in a world that is profoundly different from 1947, when the CIA was founded," Schiff said.
Training
The CIA established its first training facility, the Office of Training and Education, in 1950. Following the end of the Cold War, the CIA's training budget was slashed, which had a negative effect on employee retention. In response, Director of Central Intelligence George Tenet established CIA University in 2002. CIA University holds between 200 and 300 courses each year, training both new hires and experienced intelligence officers, as well as CIA support staff. The facility works in partnership with the National Intelligence University, and includes the Sherman Kent School for Intelligence Analysis, the Directorate of Analysis' component of the university.
For later stage training of student operations officers, there is at least one classified training area at Camp Peary, near Williamsburg, Virginia. Students are selected, and their progress evaluated, in ways derived from the OSS, published as the book Assessment of Men, Selection of Personnel for the Office of Strategic Services. Additional mission training is conducted at Harvey Point, North Carolina.
The primary training facility for the Office of Communications is Warrenton Training Center, located near Warrenton, Virginia. The facility was established in 1951 and has been used by the CIA since at least 1955.
Budget
Details of the overall United States intelligence budget are classified. Under the Central Intelligence Agency Act of 1949, the Director of Central Intelligence is the only federal government employee who can spend "un-vouchered" government money. The government showed its 1997 budget was $26.6 billion for the fiscal year. The government has disclosed a total figure for all non-military intelligence spending since 2007; the fiscal 2013 figure is $52.6 billion. According to the 2013 mass surveillance disclosures, the CIA's fiscal 2013 budget is $14.7 billion, 28% of the total and almost 50% more than the budget of the National Security Agency. CIA's HUMINT budget is $2.3 billion, the SIGINT budget is $1.7 billion, and spending for security and logistics of CIA missions is $2.5 billion. "Covert action programs," including a variety of activities such as the CIA's drone fleet and anti-Iranian nuclear program activities, accounts for $2.6 billion.
There were numerous previous attempts to obtain general information about the budget. As a result, reports revealed that CIA's annual budget in Fiscal Year 1963 was $550 million (inflation-adjusted US$ 4.6 billion in 2020), and the overall intelligence budget in FY 1997 was US $26.6 billion (inflation-adjusted US$ 42.4 billion in 2020). There have been accidental disclosures; for instance, Mary Margaret Graham, a former CIA official and deputy director of national intelligence for collection in 2005, said that the annual intelligence budget was $44 billion, and in 1994 Congress accidentally published a budget of $43.4 billion (in 2012 dollars) in 1994 for the non-military National Intelligence Program, including $4.8 billion for the CIA. After the Marshall Plan was approved, appropriating $13.7 billion over five years, 5% of those funds or $685 million were made available to the CIA.
Employees
Polygraphing
Robert Baer, a CNN analyst and former CIA operative, stated that normally a CIA employee undergoes a polygraph examination every three to four years.
Relationship with other intelligence agencies
The CIA acts as the primary US HUMINT and general analytic agency, under the Director of National Intelligence, who directs or coordinates the 16 member organizations of the United States Intelligence Community. In addition, it obtains information from other U.S. government intelligence agencies, commercial information sources, and foreign intelligence services.
U.S. agencies
CIA employees form part of the National Reconnaissance Office (NRO) workforce, created as a joint office of the CIA and US Air Force to operate the spy satellites of the US military.
The Special Collections Service is a joint CIA and National Security Agency (NSA) office that conducts clandestine electronic surveillance in embassies and hostile territory throughout the world.
Foreign intelligence services
The role and functions of the CIA are roughly equivalent to those of Germany's Federal Intelligence Service (BND), the United Kingdom's Secret Intelligence Service (the SIS or MI6), the Australian Secret Intelligence Service (ASIS), the French foreign intelligence service Direction générale de la Sécurité extérieure (DGSE), the Russian Foreign Intelligence Service (Sluzhba Vneshney Razvedki, SVR), the Chinese Ministry of State Security (MSS), the Indian Research and Analysis Wing (RAW), the Pakistani Inter-Services Intelligence (ISI), the Egyptian General Intelligence Service, Israel's Mossad, and South Korea's National Intelligence Service (NIS). While the preceding agencies both collect and analyze information, some like the U.S. State Department's Bureau of Intelligence and Research are purely analytical agencies.
The CIA was instrumental in the establishment of intelligence services in several U.S. allied countries, including Germany's BND.
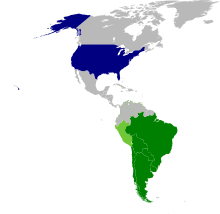
The closest links of the U.S. IC to other foreign intelligence agencies are to Anglophone countries: Australia, Canada, New Zealand, and the United Kingdom. Special communications signals that intelligence-related messages can be shared with these four countries. An indication of the United States' close operational cooperation is the creation of a new message distribution label within the main U.S. military communications network. Previously, the marking of NOFORN (i.e., No Foreign Nationals) required the originator to specify which, if any, non-U.S. countries could receive the information. A new handling caveat, USA/AUS/CAN/GBR/NZL Five Eyes, used primarily on intelligence messages, gives an easier way to indicate that the material can be shared with Australia, Canada, United Kingdom, and New Zealand.
The task of the division called "Verbindungsstelle 61" of the German Bundesnachrichtendienst is keeping contact to the CIA office in Wiesbaden. Ireland's Directorate of Military Intelligence liaises with the CIA, although it is not a member of the Five Eyes.
History
The Central Intelligence Agency was created on July 26, 1947 when Harry S. Truman signed the National Security Act into law. A major impetus for the creation of the agency was growing tensions with the USSR following the end of World War II.
Immediate predecessors
The success of the British Commandos during World War II prompted U.S. President Franklin D. Roosevelt to authorize the creation of an intelligence service modeled after the British Secret Intelligence Service (MI6), and Special Operations Executive. This led to the creation of the Office of Strategic Services (OSS) established by a Presidential military order issued by President Roosevelt on June 13, 1942. On September 20, 1945, shortly after the end of World War II, Harry S Truman signed an executive order dissolving the OSS, and by October 1945 its functions had been divided between the Departments of State and War. The division lasted only a few months. The first public mention of the "Central Intelligence Agency" appeared on a command-restructuring proposal presented by Jim Forrestal and Arthur Radford to the U.S. Senate Military Affairs Committee at the end of 1945. Despite opposition from the military establishment, the United States Department of State and the Federal Bureau of Investigation (FBI), Truman established the National Intelligence Authority in January 1946. Its operational extension was known as the Central Intelligence Group (CIG), which was the direct predecessor of the CIA.
National Security Act
Lawrence Houston, head counsel of the SSU, CIG, and, later CIA, was principal draftsman of the National Security Act of 1947, which dissolved the NIA and the CIG, and established both the National Security Council and the Central Intelligence Agency. In 1949 Houston helped to draft the Central Intelligence Agency Act (Public law 81-110), which authorized the agency to use confidential fiscal and administrative procedures, and exempted it from most limitations on the use of Federal funds. It also exempted the CIA from having to disclose its "organization, functions, officials, titles, salaries, or numbers of personnel employed." It created the program "PL-110" to handle defectors and other "essential aliens" who fell outside normal immigration procedures.
Intelligence vs. action
At the outset of the Korean War the CIA still only had a few thousand employees, around one thousand of whom worked in analysis. Intelligence primarily came from the Office of Reports and Estimates, which drew its reports from a daily take of State Department telegrams, military dispatches, and other public documents. The CIA still lacked its intelligence gathering abilities. On August 21, 1950, shortly after the invasion of South Korea, Truman announced Walter Bedell Smith as the new Director of the CIA to correct what was seen as a grave failure of Intelligence.
The CIA had different demands placed on it by the various bodies overseeing it. Truman wanted a centralized group to organize the information that reached him, the Department of Defense wanted military intelligence and covert action, and the State Department wanted to create global political change favorable to the US. Thus the two areas of responsibility for the CIA were covert action and covert intelligence. One of the main targets for intelligence gathering was the Soviet Union, which had also been a priority of the CIA's predecessors.
The United States Air Force general Hoyt Vandenberg, the CIG's second director, created the Office of Special Operations (OSO), as well as the Office of Reports and Estimates (ORE). Initially the OSO was tasked with spying and subversion overseas with a budget of $15 million, the largesse of a small number of patrons in Congress. Vandenberg's goals were much like the ones set out by his predecessor; finding out "everything about the Soviet forces in Eastern and Central Europe – their movements, their capabilities, and their intentions."
On June 18, 1948, the National Security Council issued Directive 10/2 calling for covert action against the USSR, and granting the authority to carry out covert operations against "hostile foreign states or groups" that could, if needed, be denied by the U.S. government. To this end, the Office of Policy Coordination (OPC) was created inside the new CIA. The OPC was unique; Frank Wisner, the head of the OPC, answered not to the CIA Director, but to the secretaries of defense, state, and the NSC and the OPC's actions were a secret even from the head of the CIA. Most CIA stations had two station chiefs, one working for the OSO, and one working for the OPC.
The early track record of the CIA was poor, with the agency unable to provide sufficient intelligence about the Soviet takeovers of Romania and Czechoslovakia, the Soviet blockade of Berlin, and the Soviet atomic bomb project. In particular, the agency failed to predict the Chinese entry into the Korean War with 300,000 troops. The famous double agent Kim Philby was the British liaison to American Central Intelligence. Through him, the CIA coordinated hundreds of airdrops inside the iron curtain, all compromised by Philby. Arlington Hall, the nerve center of CIA cryptanalysis, was compromised by Bill Weisband, a Russian translator and Soviet spy.
However, the CIA was successful in influencing the 1948 Italian election in favor of the Christian Democrats. The $200 million Exchange Stabilization Fund, earmarked for the reconstruction of Europe, was used to pay wealthy Americans of Italian heritage. Cash was then distributed to Catholic Action, the Vatican's political arm, and directly to Italian politicians. This tactic of using its large fund to purchase elections was frequently repeated in the subsequent years.
Korean War
At the beginning of the Korean War, CIA officer Hans Tofte claimed to have turned a thousand North Korean expatriates into a guerrilla force tasked with infiltration, guerrilla warfare, and pilot rescue. In 1952 the CIA sent 1,500 more expatriate agents north. Seoul station chief Albert Haney would openly celebrate the capabilities of those agents, and the information they sent. In September 1952 Haney was replaced by John Limond Hart, a Europe veteran with a vivid memory for bitter experiences of misinformation. Hart was suspicious of the parade of successes reported by Tofte and Haney and launched an investigation which determined that the entirety of the information supplied by the Korean sources was false or misleading. After the war, internal reviews by the CIA would corroborate Hart's findings. The CIA's Seoul station had 200 officers, but not a single speaker of Korean. Hart reported to Washington that Seoul station was hopeless, and could not be salvaged. Loftus Becker, Deputy Director of Intelligence, was sent personally to tell Hart that the CIA had to keep the station open to save face. Becker returned to Washington, pronounced the situation to be "hopeless," and that, after touring the CIA's Far East operations, the CIA's ability to gather intelligence in the far east was "almost negligible". He then resigned. Air Force Colonel James Kallis stated that CIA director Allen Dulles continued to praise the CIA's Korean force, despite knowing that they were under enemy control. When China entered the war in 1950, the CIA attempted a number of subversive operations in the country, all of which failed due to the presence of double agents. Millions of dollars were spent in these efforts. These included a team of young CIA officers airdropped into China who were ambushed, and CIA funds being used to set up a global heroin empire in Burma's Golden Triangle following a betrayal by another double agent.
1953 Iranian coup d'état
In 1951, Mohammad Mosaddegh, a member of the National Front, was elected Iranian prime-minister. As prime minister, he nationalized the Anglo-Iranian Oil Company which his predecessor had supported. The nationalization of the British-funded Iranian oil industry, including the largest oil refinery in the world, was disastrous for Mossadeq. A British naval embargo closed the British oil facilities, which Iran had no skilled workers to operate. In 1952, Mosaddegh resisted the royal refusal to approve his Minister of War and resigned in protest. The National Front took to the streets in protest. Fearing a loss of control, the military pulled its troops back five days later, and Shah Mohammad Reza Pahlavi gave in to Mosaddegh's demands. Mosaddegh quickly replaced military leaders loyal to the Shah with those loyal to him, giving him personal control over the military. Given six months of emergency powers, Mosaddegh unilaterally passed legislation. When that six months expired, his powers were extended for another year. In 1953, Mossadegh dismissed parliament and assumed dictatorial powers. This power grab triggered the Shah to exercise his constitutional right to dismiss Mosaddegh. Mosaddegh launched a military coup as the Shah fled the country. Under CIA Director Allen Dulles, Operation Ajax was put into motion. Its goal was to overthrow Mossadegh with military support from General Fazlollah Zahedi and install a pro-western regime headed by the Shah of Iran. Kermit Roosevelt Jr. oversaw the operation in Iran. On August 16, his new inner military circle protected a CIA paid mob led by Ayatollah Ruhollah Khomeini would spark what a US embassy officer called "an almost spontaneous revolution" but Mosaddegh, and the CIA had been unable to gain influence within the Iranian military. Their chosen man, former general Fazlollah Zahedi, had no troops to call on. After the failure of the first coup, Roosevelt paid demonstrators to pose as communists and deface public symbols associated with the Shah. This August 19 incident helped foster public support of the Shah and led gangs of citizens on a spree of violence intent on destroying Mossadegh. An attack on his house would force Mossadegh to flee. He surrendered the next day, and his coup came to an end.
1954 Guatemalan coup d'état
The return of the Shah to power, and the impression, cultivated by Allen Dulles, that an effective CIA had been able to guide that nation to friendly and stable relations with the West triggered planning for Operation PBSuccess, a plan to overthrow Guatemalan President Jacobo Arbenz. The plan was exposed in major newspapers before it happened after a CIA agent left plans for the coup in his Guatemala City hotel room.
The Guatemalan Revolution of 1944–54 overthrew the U.S. backed dictator Jorge Ubico and brought a democratically elected government to power. The government began an ambitious agrarian reform program attempting to grant land to millions of landless peasants. This program threatened the land holdings of the United Fruit Company, who lobbied for a coup by portraying these reforms as communist.
On June 18, 1954, Carlos Castillo Armas led 480 CIA-trained men across the border from Honduras into Guatemala. The weapons had also come from the CIA. The CIA also mounted a psychological campaign to convince the Guatemalan people and government that Armas' victory was a fait accompli, the largest part of which was a radio broadcast entitled "The Voice of Liberation" which announced that Guatemalan exiles led by Castillo Armas were shortly about to liberate the country. On June 25, a CIA plane bombed Guatemala City, destroying the government's main oil reserves. Árbenz ordered the army to distribute weapons to local peasants and workers. The army refused, forcing Jacobo Árbenz's resignation on June 27, 1954. Árbenz handed over power to Colonel Carlos Enrique Diaz. The CIA then orchestrated a series of power transfers that ended with the confirmation of Castillo Armas as president in July 1954. Armas was the first in a series of military dictators that would rule the country, triggering the brutal Guatemalan Civil War in which some 200,000 people were killed, mostly by the U.S.-backed military.
Syria
In 1949, Colonel Adib Shishakli rose to power in Syria in a CIA-backed coup. Four years later, he would be overthrown by the military, Ba'athists, and communists. The CIA and MI6 started funding right-wing members of the military but suffered a huge setback in the aftermath of the Suez Crisis. CIA Agent Rocky Stone, who had played a minor role in the Iranian Revolution, was working at the Damascus embassy as a diplomat but was the station chief. Syrian officers on the CIA dole quickly appeared on television stating that they had received money from "corrupt and sinister Americans" "in an attempt to overthrow the legitimate government of Syria." Syrian forces surrounded the embassy and rousted Agent Stone, who confessed and subsequently made history as the first American diplomat expelled from an Arab nation. This strengthened ties between Syria and Egypt, helping establish the United Arab Republic, and poisoning the well for the US for the foreseeable future.
Indonesia
The charismatic leader of Indonesia was President Sukarno. His declaration of neutrality in the Cold War put the suspicions of the CIA on him. After Sukarno hosted Bandung Conference, promoting the Non-Aligned Movement, the Eisenhower White House responded with NSC 5518 authorizing "all feasible covert means" to move Indonesia into the Western sphere.
The US had no clear policy on Indonesia. Eisenhower sent his special assistant for security operations, F. M. Dearborn Jr., to Jakarta. His report that there was high instability, and that the US lacked stable allies, reinforced the domino theory. Indonesia suffered from what he described as "subversion by democracy". The CIA decided to attempt another military coup in Indonesia, where the Indonesian military was trained by the US, had a strong professional relationship with the US military, had a pro-American officer corps that strongly supported their government, and a strong belief in civilian control of the military, instilled partly by its close association with the US military.
On September 25, 1957, Eisenhower ordered the CIA to start a revolution in Indonesia with the goal of regime change. Three days later, Blitz, a Soviet-controlled weekly in India, reported that the US was plotting to overthrow Sukarno. The story was picked up by the media in Indonesia. One of the first parts of the operation was an 11,500-ton US Navy ship landing at Sumatra, delivering weapons for as many as 8,000 potential revolutionaries.
The CIA described Agent Al Pope's bombing and strafing of Indonesia in a CIA B-26 to the President as attacks by "dissident planes." Pope's B-26 was shot down over Ambon, Indonesia on May 18, 1958, and he bailed out. When he was captured, the Indonesian military found his personnel records, after-action reports, and his membership card for the officer's club at Clark Field. On March 9, Foster Dulles, the Secretary of State, and brother of DCI Allen Dulles made a public statement calling for a revolt against communist despotism under Sukarno. Three days later, the CIA reported to the White House that the Indonesian Army's actions against the CIA-instigated revolution were suppressing communism.
After Indonesia, Eisenhower displayed mistrust of both the CIA and its Director, Allen Dulles. Dulles too displayed mistrust of the CIA itself. Abbot Smith, a CIA analyst who later became chief of the Office of National Estimates, said, "We had constructed for ourselves a picture of the USSR, and whatever happened had to be made to fit into this picture. Intelligence estimators can hardly commit a more abominable sin." On December 16, Eisenhower received a report from his intelligence board of consultants that said the agency was "incapable of making objective appraisals of its own intelligence information as well as its own operations."
Democratic Republic of the Congo
In the election of Patrice Lumumba, and his acceptance of Soviet support the CIA saw another possible Cuba. This view swayed the White House. Eisenhower ordered that Lumumba be "eliminated." The CIA delivered a quarter of a million dollars to Joseph Mobutu, their favored Congolese political figure. Mobutu delivered Lumumba to the Belgians, the former colonial masters of Congo, who executed him in short order.
Gary Powers U-2 shootdown
After the Bomber gap came the Missile Gap. Eisenhower wanted to use the U-2 to disprove the Missile Gap, but he had banned U-2 overflights of the USSR after meeting Secretary Khrushchev at Camp David. Another reason the President objected to the use of the U-2 was that, in the nuclear age, the intelligence he needed most was on their intentions, without which, the US would face a paralysis of intelligence. He was particularly worried that U-2 flights could be seen as preparations for first-strike attacks. He had high hopes for an upcoming meeting with Khrushchev in Paris. Eisenhower finally gave into CIA pressure to authorize a 16-day window for flights, which was extended an additional six days because of poor weather. On May 1, 1960, the USSR shot down a U-2 flying over the Soviet territory. To Eisenhower, the ensuing coverup destroyed his perceived honesty and his hope of leaving a legacy of thawing relations with Khrushchev. It would also mark the beginning of a long downward slide in the credibility of the Office of the President of the United States. Eisenhower later said that the U-2 coverup was the greatest regret of his presidency.
Dominican Republic
The human rights abuses of Generalissimo Rafael Trujillo had a history of more than three decades, but in August 1960 the United States severed diplomatic relations. The CIA's Special group had decided to arm Dominicans in hopes of an assassination. The CIA had dispersed three rifles and three .38 revolvers, but things paused as Kennedy assumed office. An order approved by Kennedy resulted in the dispersal of four machine guns. Trujillo died from gunshot wounds two weeks later. In the aftermath, Robert Kennedy wrote that the CIA had succeeded where it had failed many times in the past, but in the face of that success, it was caught flatfooted, having failed to plan what to do next.
Bay of Pigs
The CIA welcomed Fidel Castro on his visit to DC, and gave him a face-to-face briefing. The CIA hoped that Castro would bring about a friendly democratic government, and planned to curry his favor with money and guns. On December 11, 1959, a memo reached the DCI's desk recommending Castro's "elimination." Dulles replaced the word "elimination" with "removal," and set the wheels in motion. By mid-August 1960, Dick Bissell would seek, with the blessing of the CIA, to hire the Mafia to assassinate Castro.
The Bay of Pigs Invasion was a failed military invasion of Cuba undertaken by the CIA-sponsored paramilitary group Brigade 2506 on April 17, 1961. A counter-revolutionary military, trained and funded by the CIA, Brigade 2506 fronted the armed wing of the Democratic Revolutionary Front (DRF) and intended to overthrow the increasingly communist government of Fidel Castro. Launched from Guatemala, the invading force was defeated within three days by the Cuban Revolutionary Armed Forces, under the direct command of Prime Minister Fidel Castro. US President Dwight D. Eisenhower was concerned at the direction Castro's government was taking, and in March 1960, Eisenhower allocated $13.1 million to the CIA to plan Castro's overthrow. The CIA proceeded to organize the operation with the aid of various Cuban counter-revolutionary forces, training Brigade 2506 in Guatemala. Over 1,400 paramilitaries set out for Cuba by boat on April 13. Two days later on April 15, eight CIA-supplied B-26 bombers attacked Cuban airfields. On the night of April 16, the main invasion landed in the Bay of Pigs, but by April 20, the invaders finally surrendered. The failed invasion strengthened the position of Castro's leadership as well as his ties with the USSR. This led eventually to the events of the Cuban Missile Crisis of 1962. The invasion was a major embarrassment for US foreign policy. US President John F. Kennedy ordered a number of internal investigations across Latin America.
The Taylor Board was commissioned to determine what went wrong in Cuba. The Board came to the same conclusion that the Jan '61 President's Board of Consultants on Foreign Intelligence Activities had concluded, and many other reviews prior, and to come, that Covert Action had to be completely isolated from intelligence and analysis. The Inspector General of the CIA investigated the Bay of Pigs. He concluded that there was a need to improve the organization and management of the CIA drastically. The Special Group (Later renamed the 303 Committee) was convened in an oversight role.
Cuba: Sabotage and Terrorism
After the failure of the attempted invasion at the Bay of Pigs, the CIA proposed a program of sabotage and terrorist attacks against civilian and military targets in Cuba, with the stated intent to bring down the Cuban administration and institute a new government. It was authorized by the president in November 1961. The operation saw the CIA engage in an extensive campaign of terrorist attacks against civilians and economic targets, killing significant numbers of civilians, and carry out covert operations against the Cuban government.
The CIA established a base for the operation in Miami, given the cryptonym JMWAVE. The operation was so extensive that it housed the largest number of CIA officers outside of Langley. It was a major employer in Florida, with several thousand agents in clandestine pay of the agency.
The terrorist activities carried out by agents armed, organized and sponsored by the CIA were a further source of tension between the U.S. and Cuban governments. They were a major factor contributing to the Soviet decision to place missiles on Cuba, leading to the Cuban missile crisis.
The attacks continued through 1965. Though the level of terrorist activity directed by the CIA lessened in the second half of the 1960s, in 1969 the CIA was directed to intensify its operations against Cuba. Exile terrorists were still in the employ of the CIA in the mid-1970s, including those responsible for the Cubana 455 bombing, the worst instance of airline terrorism in the western hemisphere prior to the attacks of September 2001 in New York. Despite the large number of civilians killed in the CIA's terrorist attacks, by the measure of its stated objective the project was a complete failure.
Early Cold War, 1953–1966
The CIA was involved in anti-Communist activities in Burma, Guatemala, and Laos. There have been suggestions that the Soviet attempt to put missiles into Cuba came, indirectly, when they realized how badly they had been compromised by a US–UK defector in place, Oleg Penkovsky. One of the most significant operations ever undertaken by the CIA was directed at Zaïre in support of general-turned-dictator Mobutu Sese Seko.
Brazil
The CIA and the United States government were involved in the 1964 Brazilian coup d'état. The coup occurred from March 31 to April 1, which resulted in the Brazilian Armed Forces ousting President João Goulart. The United States saw Goulart as a left-wing threat in Latin America. Secret cables written by the US Ambassador to Brazil, Lincoln Gordon, confirmed that the CIA was involved in covert action in Brazil. The CIA encouraged "pro-democracy street rallies" in Brazil, for instance, to create dissent against Goulart.
Indochina, Tibet and the Vietnam War (1954–1975)
The OSS Patti mission arrived in Vietnam near the end of World War II, and had significant interaction with the leaders of many Vietnamese factions, including Ho Chi Minh.
The CIA Tibetan program consisted of political plots, propaganda distribution, and paramilitary and intelligence gathering based on U.S. commitments made to the Dalai Lama in 1951 and 1956.
During the period of U.S. combat involvement in the Vietnam War, there was considerable argument about progress among the Department of Defense under Robert McNamara, the CIA, and, to some extent, the intelligence staff of Military Assistance Command Vietnam.
Sometime between 1959 and 1961, the CIA started Project Tiger, a program of dropping South Vietnamese agents into North Vietnam to gather intelligence. These were failures; the Deputy Chief for Project Tiger, Captain Do Van Tien, admitted that he was an agent for Hanoi.
Johnson
In the face of the failure of Project Tiger, the Pentagon wanted CIA paramilitary forces to participate in their Op Plan 64A, this resulted in the CIA's foreign paramilitaries being put under the command of the DOD, a move seen as a slippery slope inside the CIA, a slide from covert action towards militarization.
The antiwar movement rapidly expanded across the United States during the Johnson presidency. Johnson wanted CIA Director Richard Helms to substantiate Johnson's hunch that Moscow and Beijing were financing and influencing the American antiwar movement. Thus, in the fall of 1967, the CIA launched a domestic surveillance program code-named Chaos that would linger for a total of seven years. Police departments across the country cooperated in tandem with the agency, amassing a "computer index of 300,000 names of American people and organizations, and extensive files on 7,200 citizens." Helms hatched a "Special Operations Group" in which "[eleven] CIA officers grew long hair, learned the jargon of the New Left, and went off to infiltrate peace groups in the United States and Europe."
A CIA analyst's assessment of Vietnam was that the US was "becoming progressively divorced from reality... [and] proceeding with far more courage than wisdom".
Nixon
In 1971, the NSA and CIA were engaged in domestic spying. The DOD was eavesdropping on Kissinger. The White House and Camp David were wired for sound. Nixon and Kissinger were eavesdropping on their aides, as well as reporters. Famously, Nixon's Plumbers had in their number many former CIA agents, including Howard Hunt, Jim McCord, and Eugenio Martinez. On July 7, 1971, John Ehrlichman, Nixon's domestic policy chief, told DCI Cushman, Nixon's hatchet-man in the CIA, to let Cushman "know that [Hunt] was, in fact, doing some things for the President... you should consider he has pretty much carte blanche" Importantly, this included a camera, disguises, a voice-altering device, and ID papers furnished by the CIA, as well as the CIA's participation developing film from the burglary Hunt staged on the office of Pentagon Papers leaker Daniel Ellsberg's psychologist.
On June 17, Nixon's Plumbers were caught burglarizing the DNC offices in the Watergate. On June 23, DCI Helms was ordered by the White House to wave the FBI off using national security as a pretext. The new DCI, Walters, another Nixon hack, called the acting director of the FBI and told him to drop the investigation as ordered. On June 26, Nixon's counsel John Dean ordered DCI Walters to pay the plumbers untraceable hush money. The CIA was the only part of the government that had the power to make off the book payments, but it could only be done on the orders of the CI, or, if he was out of the country, the DCI. The Acting Director of the FBI started breaking ranks. He demanded the CIA produce a signed document attesting to the national security threat of the investigation. Jim McCord's lawyer contacted the CIA informing them that McCord had been offered a Presidential pardon if he fingered the CIA, testifying that the break-in had been an operation of the CIA. Nixon had long been frustrated by what he saw as a liberal infection inside the CIA and had been trying for years to tear the CIA out by its roots. McCord wrote "If [DCI] Helms goes (takes the fall) and the Watergate operation is laid at the CIA's feet, where it does not belong, every tree in the forest will fall. It will be a scorched desert."
On November 13, after Nixon's landslide re-election, Nixon told Kissinger "[I intend] to ruin the Foreign Service. I mean ruin it – the old Foreign Service – and to build a new one." He had similar designs for the CIA and intended to replace Helms with James Schlesinger. Nixon had told Helms that he was on the way out, and promised that Helms could stay on until his 60th birthday, the mandatory retirement age. On February 2, Nixon broke that promise, carrying through with his intention to "remove the deadwood" from the CIA. "Get rid of the clowns" was his order to the incoming CI. Kissinger had been running the CIA since the beginning of Nixon's presidency, but Nixon impressed on Schlesinger that he must appear to Congress to be in charge, averting their suspicion of Kissinger's involvement. Nixon also hoped that Schlesinger could push through broader changes in the intelligence community that he had been working towards for years, the creation of a Director of National Intelligence, and spinning off the covert action part of the CIA into a separate organ. Before Helms would leave office, he would destroy every tape he had secretly made of meetings in his office, and many of the papers on Project MKUltra. In Schlesinger's 17-week tenure, in his assertion to President Nixon that it was "imperative to cut back on 'the prominence of CIA operations' around the world," the director fired more than 1,500 employees. As Watergate threw the spotlight on the CIA, Schlesinger, who had been kept in the dark about the CIA's involvement, decided he needed to know what skeletons were in the closet. He issued a memo to every CIA employee directing them to disclose to him any CIA activity they knew of past or present that could fall outside the scope of the CIA's charter.
This became the Family Jewels. It included information linking the CIA to the assassination of foreign leaders, the illegal surveillance of some 7,000 U.S. citizens involved in the antiwar movement (Operation CHAOS), the CIA had also experimented on U.S. and Canadian citizens without their knowledge, secretly giving them LSD (among other things) and observing the results. This prompted Congress to create the Church Committee in the Senate, and the Pike Committee in the House. President Gerald Ford created the Rockefeller Commission, and issued an executive order prohibiting the assassination of foreign leaders. DCI Colby leaked the papers to the press, later he stated that he believed that providing Congress with this information was the correct thing to do, and ultimately in the CIA's interests.
Congressional Investigations
Acting Attorney General Laurence Silberman learned of the existence of the Family Jewels and issued a subpoena for them, prompting eight congressional investigations on the domestic spying activities of the CIA. Bill Colby's short tenure as DCI would end with the Halloween Massacre. His replacement was George H.W. Bush. At the time, the DOD had control of 80% of the intelligence budget.
Communication and coordination between the CIA and the DOD would suffer greatly under Defense Secretary Donald Rumsfeld. The CIA's budget for hiring clandestine officers had been squeezed out by the paramilitary operations in south-east Asia, and the government's poor popularity further strained hiring. This left the agency bloated with middle management, and anemic in younger officers. With employee training taking five years, the agency's only hope would be on the trickle of new officers coming to fruition years in the future. The CIA would see another setback as communists would take Angola. William J. Casey, a member of Ford's Intelligence Advisory Board, obtained Bush's approval to allow a team from outside the CIA to produce Soviet military estimates as a "Team B." The "B" team was composed of hawks. Their estimates were the highest that could be justified, and they painted a picture of a growing Soviet military when the Soviet military was indeed shrinking. Many of their reports found their way to the press. As a result of the investigations, congressional oversight of the CIA eventually evolved into a select intelligence committee in the House, and Senate supervising covert actions authorized by the President.
Chad
Chad's neighbor Libya was a major source of weaponry to communist rebel forces. The CIA seized the opportunity to arm and finance Chad's Prime Minister, Hissène Habré, after he created a breakaway government in Western Sudan, even giving him Stinger missiles.
Afghanistan
In Afghanistan, the CIA funneled $40 billion worth of weapons, which included over two thousand FIM-92 Stinger surface-to-air missiles, to Pakistani Inter-Services Intelligence (ISI), which funneled them to almost 100,000 Afghan resistance fighters, notably the Mujahideen, and foreign "Afghan Arabs" from forty Muslim countries.
Iran/Contra
Under President Jimmy Carter, the CIA was conducting covertly funded pro-American opposition against the Sandinista. In March 1981, Reagan told Congress that the CIA would protect El Salvador by preventing the shipment of Nicaraguan arms into the country to arm Communist rebels. This was a ruse. The CIA was arming and training Nicaraguans Contras in Honduras in hopes that they could depose the Sandinistas in Nicaragua. Through the intelligence branch of the CIA supported William J. Casey's tenure as DCI little of what he said in the National Security Planning Group, or to President Reagan, so Casey formed the Central American Task Force, staffed with yes men from Covert Action. On December 21, 1982, Congress passed a law restricting the CIA to its stated mission, restricting the flow of arms from Nicaragua to El Salvador, prohibiting the use of funds to oust the Sandinistas. Reagan testified before Congress, assuring them that the CIA was not trying to topple the Nicaraguan governmentLebanon
The CIA's prime source in Lebanon was Bashir Gemayel, a member of the Christian Maronite sect. The uprising against the Maronite minority blinded the CIA. Israel invaded Lebanon, and, along with the CIA, propped up Gemayel. This got Gemayel's assurance that Americans would be protected in Lebanon. Thirteen days later he was assassinated. Imad Mughniyah, a Hezbollah assassin would target Americans in retaliation for the Israeli invasion, the Sabra and Shatila massacre, and the US Marines of the Multi-National Force for their role in opposing the PLO in Lebanon. On April 18, 1983, a 2,000 lb car bomb exploded in the lobby of the American embassy in Beirut, killing 63 people including 17 Americans, and 7 CIA officers, including Robert Ames, one of the CIA's best Middle East experts. America's fortunes in Lebanon would only suffer more as America's poorly-directed retaliation for the bombing was interpreted by many as support for the Christian Maronite minority. On October 23, 1983, two bombs (1983 Beirut Bombing) were set off in Beirut, including a 10-ton bomb at a US military barracks that killed 242 people.
The Embassy bombing had taken the life of the CIA's Beirut Station Chief, Ken Haas. Bill Buckley was sent in to replace him. Eighteen days after the US Marines left Lebanon, Buckley was kidnapped. On March 7, 1984, Jeremy Levin, CNN Bureau Chief in Beirut was kidnapped. Twelve more Americans would be captured in Beirut during the Reagan Administration. Manucher Ghorbanifar, a former Savak agent was an information seller, and the subject of a rare CIA burn notice for his track record of misinformation. He reached out to the agency offering a back channel to Iran, suggesting a trade of missiles that would be lucrative to the intermediaries.
Pakistan
It has been alleged by such authors as Ahmed Rashid that the CIA and ISI have been waging a clandestine war. The Afghan Taliban – with whom the United States is officially in conflict – is headquartered in Pakistan's Federally Administered Tribal Areas and according to some reports is largely funded by the ISI. The Pakistani government denies this.
India–Pakistan geopolitical tensions
On May 11, 1998, CIA Director George Tenet and his agency were taken aback by India's second nuclear test. The bellicose gesture ruffled the feathers of its nuclear-capable adversary, Pakistan, and, furthermore, "remade the balance of power in the world." The nuclear test was New Delhi's calculated response to Pakistan previously testing new missiles in its expanding arsenal. This seismic series of events subsequently revealed the CIA's "failure of espionage, a failure to read photographs, a failure to comprehend reports, a failure to think, and a failure to see."
Poland 1980–1989
Unlike the Carter Administration, the Reagan Administration supported the Solidarity movement in Poland, and – based on CIA intelligence – waged a public relations campaign to deter what the Carter administration felt was "an imminent move by large Soviet military forces into Poland." Colonel Ryszard Kukliński, a senior officer on the Polish General Staff, was secretly sending reports to the CIA. The CIA transferred around $2 million yearly in cash to Solidarity, which suggests that $10 million total is a reasonable estimate for the five-year total. There were no direct links between the CIA and Solidarnosc, and all money was channeled through third parties. CIA officers were barred from meeting Solidarity leaders, and the CIA's contacts with Solidarnosc activists were weaker than those of the AFL-CIO, which raised 300 thousand dollars from its members, which were used to provide material and cash directly to Solidarity, with no control of Solidarity's use of it. The U.S. Congress authorized the National Endowment for Democracy to promote democracy, and the NED allocated $10 million to Solidarity. When the Polish government launched a crackdown of its own in December 1981, however, Solidarity was not alerted. Potential explanations for this vary; some believe that the CIA was caught off guard, while others suggest that American policy-makers viewed an internal crackdown as preferable to an "inevitable Soviet intervention." CIA support for Solidarity included money, equipment and training, which was coordinated by Special Operations CIA division. U.S. House intelligence committee member, stated that USA provided "supplies and technical assistance in terms of clandestine newspapers, broadcasting, propaganda, money, organizational help and advice". Michael Reisman from Yale Law School named operations in Poland as one of the covert actions of CIA during Cold War. Initial funds for covert actions by CIA were $2 million, but soon after authorization was increased and by 1985 CIA successfully infiltrated Poland Rainer Thiel in Nested Games of External Democracy Promotion: The United States and the Polish Liberalization 1980–1989 mentions how covert operations by CIA and spy games among others allowed USA to proceed with successful regime change.
Operation Desert Storm
During the Iran-Iraq war, the CIA had backed both sides. The CIA had maintained a network of spies in Iran, but in 1989 a CIA mistake compromised every agent they had in there, and the CIA had no agents in Iraq. In the weeks before the Invasion of Kuwait, the CIA downplayed the military buildup. During the war, CIA estimates of Iraqi abilities and intentions flip-flopped and were rarely accurate. In one particular case, the DOD had asked the CIA to identify military targets to bomb. One target the CIA identified was an underground shelter. The CIA didn't know that it was a civilian bomb shelter. In a rare instance, the CIA correctly determined that the coalition forces efforts were coming up short in their efforts to destroy SCUD missiles. Congress took away the CIA's role in interpreting spy-satellite photos, putting the CIA's satellite intelligence operations under the auspices of the military. The CIA created its office of military affairs, which operated as "second-echelon support for the Pentagon... answering... questions from military men [like] 'how wide is this road?'"
Fall of the USSR
Gorbachev's announcement of the unilateral reduction of 500,000 Soviet troops took the CIA by surprise. Moreover, Doug MacEachin, the CIA's Chief of Soviet analysis said that even if the CIA had told the President, the NSC, and Congress about the cuts beforehand, it would have been ignored. "We never would have been able to publish it." All the CIA numbers on the USSR's economy were wrong. Too often the CIA relied on inexperienced people supposedly deemed experts. Bob Gates had preceded Doug MacEachin as Chief of Soviet analysis, and he had never visited Russia. Few officers, even those stationed in the country spoke the language of the people on whom they spied. And the CIA could not send agents to respond to developing situations. The CIA analysis of Russia during the entire cold war was either driven by ideology, or by politics. William J. Crowe, the Chairman of the Joint Chiefs of Staff, noted that the CIA "talked about the Soviet Union as if they weren't reading the newspapers, much less developed clandestine intelligence."
President Clinton
On January 25, 1993, Mir Qazi opened fire at the CIA headquarters in Langley, Virginia, killing two agents and wounding three others. On February 26, Al-Qaeda terrorists led by Ramzi Yousef bombed the parking garage below the North Tower of the World Trade Center in New York City, killing six people and injuring 1,402 others.
During the Bosnian War, the CIA ignored signs within and without of the Srebrenica massacre. On July 13, 1995, when the press report about the massacre came out, the CIA received pictures from spy satellite of prisoners guarded by men with guns in Srebrenica. The CIA had no agents on the ground to verify the report. Two weeks after news reports of the slaughter, the CIA sent a U-2 to photograph it. A week later the CIA completed its report on the matter. The final report came to the Oval Office on August 4, 1995. In short, it took three weeks for the agency to confirm that one of the largest mass murders in Europe since the Second World War had occurred. Another CIA mistakes in Balkan during Clinton presidency occurred in NATO bombing of Serbia. To force Slobodan Milošević to withdraw his troops from Kosovo. The CIA had been invited to provide military targets for bombings. The agency's analysts used tourist maps to fix the location. However, the agency incorrectly provided the coordinates of the Chinese Embassy as a target resulting in its bombing. The CIA had misread the target as Slobodan Milosevic 's military depot.
In France, the CIA had orders for economic intelligence; a female CIA agent revealed her connections to the CIA to the French. Dick Holm, Paris Station Chief, was expelled. In Guatemala, the CIA produced the Murphy Memo, based on audio recordings made by bugs planted by Guatemalan intelligence in the bedroom of Ambassador Marilyn McAfee. In the recording, Ambassador McAfee verbally entreated "Murphy." The CIA circulated a memo in the highest Washington circles accusing Ambassador McAfee of having an extramarital lesbian affair with her secretary, Carol Murphy. There was no affair. Ambassador McAfee was calling to Murphy, her poodle.
Harold James Nicholson would burn several serving officers and three years of trainees before he was caught spying for Russia. In 1997 the House would pen another report, which said that CIA officers know little about the language or politics of the people they spy on; the conclusion was that the CIA lacked the "depth, breadth, and expertise to monitor political, military, and economic developments worldwide." Russ Travers said in the CIA in-house journal that in five years "intelligence failure is inevitable". In 1997 the CIA's new director George Tenet would promise a new working agency by 2002. The CIA's surprise at India's detonation of an atom bomb was a failure at almost every level. After the 1998 embassy bombings by Al Qaeda, the CIA offered two targets to be hit in retaliation. One of them was the Al-Shifa pharmaceutical factory, where traces of chemical weapon precursors had been detected. In the aftermath, it was concluded that "the decision to target al Shifa continues a tradition of operating on inadequate intelligence about Sudan." It triggered the CIA to make "substantial and sweeping changes" to prevent "a catastrophic systemic intelligence failure." Between 1991 and 1998 the CIA lost 3,000 employees.
Aldrich Ames
Between 1985 and 1986, the CIA lost every spy it had in Eastern Europe. The details of the investigation into the cause were obscured from the new Director, and the investigation had little success and has been widely criticized. On February 21, 1994, FBI agents pulled Aldrich Ames out of his Jaguar. In the investigation that ensued, the CIA discovered that many of the sources for its most important analyses of the USSR were based on Soviet disinformation fed to the CIA by controlled agents. On top of that, it was discovered that, in some cases, the CIA suspected at the time that the sources were compromised, but the information was sent up the chain as genuine.
Osama bin Laden
Agency files show that it is believed Osama bin Laden was funding the Afghan rebels against the USSR in the 1980s. In 1991, bin Laden returned to his native Saudi Arabia protesting the presence of troops, and Operation Desert Storm. He was expelled from the country. In 1996, the CIA created a team to hunt bin Laden. They were trading information with the Sudanese until, on the word of a source that would later be found to be a fabricator, the CIA closed its Sudan station later that year. In 1998, bin Laden would declare war on America, and, on August 7, strike in Tanzania and Nairobi. On October 12, 2000, Al Qaeda bombed the USS Cole. In the first days of George W. Bush's presidency, Al Qaeda threats were ubiquitous in daily presidential CIA briefings, but it may have become a case of crying wolf. The agency's predictions were dire but carried little weight, and the focus of the president and his defense staff were elsewhere. The CIA arranged the arrests of suspected Al Qaeda members through cooperation with foreign agencies, but the CIA could not definitively say what effect these arrests have had, and it could not gain hard intelligence from those captured. The President had asked the CIA if Al Qaeda could plan attacks in the US. On August 6, Bush received a daily briefing with the headline, not based on current, solid intelligence, "Al Qaeda determined to strike inside the US." The US had been hunting bin Laden since 1996 and had had several opportunities, but neither Clinton, nor Bush had wanted to risk taking an active role in a murky assassination plot, and the perfect opportunity had never materialized for a DCI that would have given him the reassurances he needed to take the plunge. That day, Richard A. Clarke sent National Security Advisor Condoleezza Rice warning of the risks, and decrying the inaction of the CIA.
Al-Qaeda and the Global War on Terrorism
The CIA had long been dealing with terrorism originating from abroad, and in 1986 had set up a Counterterrorist Center to deal specifically with the problem. At first, confronted with secular terrorism, the agency found Islamist terrorism looming increasingly large on its scope.
In January 1996, the CIA created an experimental "virtual station," the Bin Laden Issue Station, under the Counterterrorist Center, to track bin Laden's developing activities. Al-Fadl, who defected to the CIA in spring 1996, began to provide the Station with a new image of the Al Qaeda leader: he was not only a terrorist financier but a terrorist organizer as well. FBI Special Agent Dan Coleman (who together with his partner Jack Cloonan had been "seconded" to the bin Laden Station) called him Qaeda's "Rosetta Stone".
In 1999, CIA chief George Tenet launched a plan to deal with al-Qaeda. The Counterterrorist Center, its new chief, Cofer Black, and the center's bin Laden unit were the plan's developers and executors. Once it was prepared, Tenet assigned CIA intelligence chief Charles E. Allen to set up a "Qaeda cell" to oversee its tactical execution. In 2000, the CIA and USAF jointly ran a series of flights over Afghanistan with a small remote-controlled reconnaissance drone, the Predator; they obtained probable photos of bin Laden. Cofer Black and others became advocates of arming the Predator with missiles to try to assassinate bin Laden and other al-Qaeda leaders. After the Cabinet-level Principals Committee meeting on terrorism of September 4, 2001, the CIA resumed reconnaissance flights, the drones now being weapons-capable.
September 11 attacks and its aftermath
On September 11, 2001, 19 Al-Qaeda members hijacked four passenger jets within the Northeastern United States in a series of coordinated terrorist attacks. Two planes crashed into the Twin Towers of the World Trade Center in New York City, the third into the Pentagon in Arlington County, Virginia, and the fourth inadvertently into a field near Shanksville, Pennsylvania. The attacks cost the lives of 2,996 people (including the 19 hijackers), caused the destruction of the Twin Towers, and damaged the western side of the Pentagon. Soon after 9/11, The New York Times released a story stating that the CIA's New York field office was destroyed in the wake of the attacks. According to unnamed CIA sources, while first responders, military personnel and volunteers were conducting rescue efforts at the World Trade Center site, a special CIA team was searching the rubble for both digital and paper copies of classified documents. This was done according to well-rehearsed document recovery procedures put in place after the Iranian takeover of the United States Embassy in Tehran in 1979. While it was not confirmed whether the agency was able to retrieve the classified information, it is known that all agents present that day fled the building safely.
While the CIA insists that those who conducted the attacks on 9/11 were not aware that the agency was operating at 7 World Trade Center under the guise of another (unidentified) federal agency, this center was the headquarters for many notable criminal terrorism investigations. Though the New York field offices' main responsibilities were to monitor and recruit foreign officials stationed at the United Nations, the field office also handled the investigations of the August 1998 bombings of United States Embassies in East Africa and the October 2000 bombing of the USS Cole. Despite the fact that the 9/11 attacks may have damaged the CIA's New York branch, and they had to loan office space from the US Mission to the United Nations and other federal agencies, there was an upside for the CIA. In the months immediately following 9/11, there was a huge increase in the number of applications for CIA positions. According to CIA representatives that spoke with The New York Times, pre-9/11 the agency received approximately 500 to 600 applications a week, in the months following 9/11 the agency received that number daily.
The intelligence community as a whole, and especially the CIA, were involved in presidential planning immediately after the 9/11 attacks. In his address to the nation at 8:30pm on September 11, 2001, George W. Bush mentioned the intelligence community: "The search is underway for those who are behind these evil acts, I've directed the full resource of our intelligence and law enforcement communities to find those responsible and bring them to justice."
The involvement of the CIA in the newly coined "War on Terror" was further increased on September 15, 2001. During a meeting at Camp David George W. Bush agreed to adopt a plan proposed by CIA director George Tenet. This plan consisted of conducting a covert war in which CIA paramilitary officers would cooperate with anti-Taliban guerillas inside Afghanistan. They would later be joined by small special operations forces teams which would call in precision airstrikes on Taliban and Al Qaeda fighters. This plan was codified on September 16, 2001, with Bush's signature of an official Memorandum of Notification that allowed the plan to proceed.
On November 25–27, 2001, Taliban prisoners revolted at the Qala Jangi prison west of Mazar-e-Sharif. Though several days of struggle occurred between the Taliban prisoners and the Northern Alliance members present, the prisoners gained the upper hand and obtained North Alliance weapons. At some point during this period Johnny "Mike" Spann, a CIA officer sent to question the prisoners, was beaten to death. He became the first American to die in combat in the war in Afghanistan.
After 9/11, the CIA came under criticism for not having done enough to prevent the attacks. Tenet rejected the criticism, citing the agency's planning efforts especially over the preceding two years. He also considered that the CIA's efforts had put the agency in a position to respond rapidly and effectively to the attacks, both in the "Afghan sanctuary" and in "ninety-two countries around the world". The new strategy was called the "Worldwide Attack Matrix".
Anwar al-Awlaki, a Yemeni-American U.S. citizen and al-Qaeda member, was killed on September 30, 2011, by an airstrike conducted by the Joint Special Operations Command. After several days of surveillance of Awlaki by the Central Intelligence Agency, armed drones took off from a new, secret American base in the Arabian Peninsula, crossed into northern Yemen, and fired several Hellfire missiles at al-Awlaki's vehicle. Samir Khan, a Pakistani-American al-Qaeda member and editor of the jihadist Inspire magazine, also reportedly died in the attack. The combined CIA/JSOC drone strike was the first in Yemen since 2002 – there have been others by the military's Special Operations forces – and was part of an effort by the spy agency to duplicate in Yemen the covert war which has been running in Afghanistan and Pakistan.
Use of vaccination program in hunt for Osama bin Laden
The agency attracted widespread criticism after it used a local doctor in Pakistan to set up a hepatitis B vaccination program in Abbottabad in 2011 to obtain DNA samples from the occupants of a compound where it was suspected bin Laden was living, hoping to obtain samples from bin Laden or his children in order to confirm his presence. It is unknown whether any useful DNA was acquired from the program, but it was deemed not successful. The doctor was later arrested and sentenced to a lengthy prison term on allegedly unrelated charges. Médecins Sans Frontières criticised the CIA for endangering and undermining trust in medical workers and The New York Times reported that the CIA's action had increased resistance to vaccination programs in Pakistan.
Failures in intelligence analysis
A major criticism is a failure to forestall the September 11 attacks. The 9/11 Commission Report identified failures in the IC as a whole. One problem, for example, was the FBI failing to "connect the dots" by sharing information among its decentralized field offices.
The report concluded that former DCI George Tenet failed to adequately prepare the agency to deal with the danger posed by al-Qaeda prior to the attacks of September 11, 2001. The report was finished in June 2005 and was partially released to the public in an agreement with Congress, over the objections of current DCI General Michael Hayden. Hayden said its publication would "consume time and attention revisiting ground that is already well plowed." Tenet disagreed with the report's conclusions, citing his planning efforts vis-à-vis al-Qaeda, particularly from 1999. Assistant Secretary of State for Intelligence, Carl W. Ford Jr. remarked, ""As long as we rate intelligence more for its volume than its quality, we will continue to turn out the $40 billion pile of crap we have become famous for." He further stated, "[The CIA is] broken. It's so broken that nobody wants to believe it."
Abuses of CIA authority, 1970s–1990s
Conditions worsened in the mid-1970s, around the time of Watergate. A dominant feature of political life during that period were the attempts of Congress to assert oversight of the U.S. Presidency and the executive branch of the U.S. government. Revelations about past CIA activities, such as assassinations and attempted assassinations of foreign leaders (most notably Fidel Castro and Rafael Trujillo) and illegal domestic spying on U.S. citizens, provided the opportunities to increase Congressional oversight of U.S. intelligence operations. CIA involvement in Contra cocaine trafficking in Nicaragua and complicity in the actions of the death squads in El Salvador and Honduras also came to light.
Hastening the CIA's fall from grace was the burglary of the Watergate headquarters of the Democratic Party by former CIA officers, and President Richard Nixon's subsequent attempt to use the CIA to impede the FBI's investigation of the burglary. In the famous "smoking gun" recording that led to President Nixon's resignation, Nixon ordered his chief of staff, H. R. Haldeman, to tell the CIA that further investigation of Watergate would "open the whole can of worms about the Bay of Pigs". In this way Nixon and Haldemann ensured that the CIA's No. 1 and No. 2 ranking officials, Richard Helms and Vernon Walters, communicated to FBI Director L. Patrick Gray that the FBI should not follow the money trail from the burglars to the Committee to Re-elect the President, as it would uncover CIA informants in Mexico. The FBI initially agreed to this due to a long-standing agreement between the FBI and CIA not to uncover each other's sources of information, though within a couple of weeks the FBI demanded this request in writing, and when no such formal request came, the FBI resumed its investigation into the money trail. Nonetheless, when the smoking gun tapes were made public, damage to the public's perception of CIA's top officials, and thus to the CIA as a whole, could not be avoided.
Repercussions from the Iran–Contra affair arms smuggling scandal included the creation of the Intelligence Authorization Act in 1991. It defined covert operations as secret missions in geopolitical areas where the U.S. is neither openly nor engaged. This also required an authorizing chain of command, including an official, presidential finding report and the informing of the House and Senate Intelligence Committees, which, in emergencies, requires only "timely notification."
Iraq War
Seventy-two days after the 9/11 attacks, President Bush told Secretary of Defense Rumsfeld to update the US plan for an invasion of Iraq, but not to tell anyone. Rumsfeld asked Bush if he could bring DCI Tenet into the loop, to which Bush agreed.
The CIA had put out feelers to Iraq in the form of eight of their best officers in Kurdish territory in Northern Iraq. These officers hit a goldmine, unprecedented in the famously closed Hussein government. By December 2002, the CIA had close to a dozen functional networks in Iraq and would penetrate Iraq's SSO, tap the encrypted communications of the Deputy Prime Minister, and recruit the bodyguard of Hussein's son as an agent. As time passed, the CIA would become more and more frantic about the possibility of their networks being compromised. To the CIA, the invasion had to occur before the end of February 2003 if their sources inside Hussein's government were to survive. The rollup would happen as predicted, 37 CIA sources recognized by their Thuraya satellite telephones provided for them by the CIA.
The case Colin Powell presented before the United Nations (purportedly proving an Iraqi WMD program) was inaccurate. DDCI John E. McLaughlin was part of a long discussion in the CIA about equivocation. McLaughlin, who would make, among others, the "slam dunk" presentation to the President, "felt that they had to dare to be wrong to be clearer in their judgments". The Al Qaeda connection, for instance, was from a single source, extracted through torture, and was later denied. Curveball was a known liar, and the sole source for the mobile chemical weapons factories. A postmortem of the intelligence failures in the lead up to Iraq led by former DDCI Richard Kerr would conclude that the CIA had been a casualty of the Cold War, wiped out in a way "analogous to the effect of the meteor strikes on the dinosaurs."
The opening days of the invasion of Iraq would see successes and defeats for the CIA. With its Iraq networks compromised, and its strategic and tactical information shallow, and often wrong, the intelligence side of the invasion itself would be a black eye for the agency. The CIA would see some success with its "Scorpion" paramilitary teams composed of CIA Special Activities Division agents, along with friendly Iraqi partisans. CIA SAD officers would also help the US 10th Special Forces. The occupation of Iraq would be a low point in the history of the CIA. At the largest CIA station in the world, agents would rotate through 1–3-month tours. In Iraq, almost 500 transient agents would be trapped inside the Green Zone while Iraq station chiefs would rotate with only a little less frequency.
2004, DNI takes over CIA top-level functions
The Intelligence Reform and Terrorism Prevention Act of 2004 created the office of the Director of National Intelligence (DNI), who took over some of the government and intelligence community (IC)-wide functions that had previously been the CIA's. The DNI manages the United States Intelligence Community and in so doing it manages the intelligence cycle. Among the functions that moved to the DNI were the preparation of estimates reflecting the consolidated opinion of the 16 IC agencies, and preparation of briefings for the president. On July 30, 2008, President Bush issued Executive Order 13470 amending Executive Order 12333 to strengthen the role of the DNI.
Previously, the Director of Central Intelligence (DCI) oversaw the Intelligence Community, serving as the president's principal intelligence advisor, additionally serving as head of the CIA. The DCI's title now is "Director of the Central Intelligence Agency" (D/CIA), serving as head of the CIA.
Currently, the CIA reports to the Director of National Intelligence. Before the establishment of the DNI, the CIA reported to the President, with informational briefings to congressional committees. The National Security Advisor is a permanent member of the National Security Council, responsible for briefing the President with pertinent information collected by all U.S. intelligence agencies, including the National Security Agency, the Drug Enforcement Administration, etc. All 16 Intelligence Community agencies are under the authority of the Director of National Intelligence.
Operation Neptune Spear
On May 1, 2011, President Barack Obama announced that Osama bin Laden was killed earlier that day by "a small team of Americans" operating in Abbottabad, Pakistan, during a CIA operation.The raid was executed from a CIA forward base in Afghanistan by elements of the U.S. Navy's Naval Special Warfare Development Group and CIA paramilitary operatives.
It resulted in the acquisition of extensive intelligence on the future attack plans of al-Qaeda.
The operation was a result of years of intelligence work that included the CIA's capture and interrogation of Khalid Sheik Mohammad, which led to the identity of a courier of bin Laden's, the tracking of the courier to the compound by Special Activities Division paramilitary operatives and the establishing of a CIA safe house to provide critical tactical intelligence for the operation.
Syrian Civil War
Under the aegis of operation Timber Sycamore and other clandestine activities, CIA operatives and U.S. special operations troops have trained and armed nearly 10,000 rebel fighters at a cost of $1 billion a year. The CIA has been sending weapons to anti-government rebels in Syria since at least 2012. These weapons have been reportedly falling into hands of extremists, such as al-Nusra Front and ISIL. Around February 2017, the CIA was instructed to halt military aid to Syrian rebels (Free Syrian Army or FSA), which also included training, ammunition, guided missiles, and salaries. Sources state that the hold on aid was not related to the transitions from Obama's administration to Trump's, but rather due to issues faced by the FSA. Based on responses by rebel officials, they believe that the aid freeze is related to concerns that weapons and funds will fall into the hands of ISIL. Based on information obtained by Reuters, five FSA groups have confirmed that they received funding and military support from a source called "MOM operations room." Several countries besides the U.S., including Turkey, Qatar, and Saudi Arabia, had also contributed to the funding of the FSA. On April 6, 2017, Al-Jazeera reported that funding to the FSA was partially restored. Based on the information provided by two FSA sources, the new military operation room will receive its funds from the coalition "Friends of Syria." The coalition consists of members from the U.S, Turkey, Western Europe, and Gulf states, which previously supported the military operation known as MOM.
It was reported in July 2017 that President Donald Trump had ordered a "phasing out" of the CIA's support for anti-Assad rebels.
Reorganization
On March 6, 2015, the office of the D/CIA issued an unclassified edition of a statement by the Director, titled "Our Agency's Blueprint for the Future," as a press release for public consumption. The press release announced sweeping plans for the reorganization and reform of the CIA, which the Director believes will bring the CIA more in line with the agency doctrine called the 'Strategic Direction.' Among the key changes disclosed include the establishment of a new directorate, the Directorate of Digital Innovation, which is responsible for designing and crafting the digital technology to be used by the agency, to keep the CIA always ahead of its enemies. The Directorate of Digital Innovation will also train CIA staff in the use of this technology, to prepare the CIA for the future, and it will also use the technological revolution to deal with cyber-terrorism and other perceived threats. The new directorate will be the chief cyber-espionage arm of the agency going forward.
Other changes which were announced include the formation of a Talent Development Center of Excellence, the enhancement and expansion of the CIA University and the creation of the office of the Chancellor to head the CIA University to consolidate and unify recruitment and training efforts. The office of the Executive Director will be empowered and expanded, and the secretarial offices serving the Executive Director will be streamlined. The restructuring of the entire Agency is to be revamped according to a new model whereby governance is modeled after the structure and hierarchy of corporations, said to increase the efficiency of workflow and to enable the Executive Director to manage day-to-day activity significantly. As well, another stated intention was to establish 'Mission Centers', each one to deal with a specific geographic region of the world, which will bring the full collaboration and joint efforts of the five Directorates together under one roof. While the Directorate heads will still retain ultimate authority over their respective Directorate, the Mission Centers will be led by an Assistant Director who will work with the capabilities and talents of all five Directorates on mission-specific goals for the parts of the world which they are given responsibility for.
The unclassified version of the document ends with the announcement that the National Clandestine Service (NCS) will be reverting to its original Directorate name, the Directorate of Operations. The Directorate of Intelligence is also being renamed. It will now be the Directorate of Analysis.
Drones
A new policy introduced by President Barack Obama removed the authority of the CIA to launch drone attacks and allowed these attacks only under Department of Defense command. This change was reversed by President Donald Trump, who authorized CIA drone strikes on suspected terrorists.
Encryption devices sold through front company
For decades until 2018, the CIA secretly owned Crypto AG, a small Swiss company that made encryption devices, in association with West German intelligence. The company sold compromised encryption devices to over 120 countries, allowing Western intelligence to eavesdrop on communications that the users believed to be secure.
Open source intelligence
Until the 2004 reorganization of the intelligence community, one of the "services of common concern" that the CIA provided was open source intelligence from the Foreign Broadcast Information Service (FBIS). FBIS, which had absorbed the Joint Publication Research Service, a military organization that translated documents, moved into the National Open Source Enterprise under the Director of National Intelligence.
During the Reagan administration, Michael Sekora (assigned to the DIA), worked with agencies across the intelligence community, including the CIA, to develop and deploy a technology-based competitive strategy system called Project Socrates. Project Socrates was designed to utilize open source intelligence gathering almost exclusively. The technology-focused Socrates system supported such programs as the Strategic Defense Initiative in addition to private sector projects.
As part of its mandate to gather intelligence, the CIA is looking increasingly online for information, and has become a major consumer of social media. "We're looking at YouTube, which carries some unique and honest-to-goodness intelligence," said Doug Naquin, director of the DNI Open Source Center (OSC) at CIA headquarters. "We're looking at chat rooms and things that didn't exist five years ago, and trying to stay ahead." CIA launched a Twitter account in June 2014.
Outsourcing and privatization
Many of the duties and functions of Intelligence Community activities, not the CIA alone, are being outsourced and privatized. Mike McConnell, former Director of National Intelligence, was about to publicize an investigation report of outsourcing by U.S. intelligence agencies, as required by Congress. However, this report was then classified. Hillhouse speculates that this report includes requirements for the CIA to report:
- different standards for government employees and contractors;
- contractors providing similar services to government workers;
- analysis of costs of contractors vs. employees;
- an assessment of the appropriateness of outsourced activities;
- an estimate of the number of contracts and contractors;
- comparison of compensation for contractors and government employees;
- attrition analysis of government employees;
- descriptions of positions to be converted back to the employee model;
- an evaluation of accountability mechanisms;
- an evaluation of procedures for "conducting oversight of contractors to ensure identification and prosecution of criminal violations, financial waste, fraud, or other abuses committed by contractors or contract personnel"; and
- an "identification of best practices of accountability mechanisms within service contracts."
According to investigative journalist Tim Shorrock:
...what we have today with the intelligence business is something far more systemic: senior officials leaving their national security and counterterrorism jobs for positions where they essentially perform the same jobs they once held at the CIA, the NSA, and other agencies – but for double or triple the salary, and profit. It's a privatization of the highest order, in which our collective memory and experience in intelligence – our crown jewels of spying, so to speak – are owned by corporate America. There is essentially no government oversight of this private sector at the heart of our intelligence empire. And the lines between public and private have become so blurred as to be nonexistent.
Congress had required an outsourcing report by March 30, 2008.
The Director of National Intelligence has been granted the authority to increase the number of positions (FTEs) on elements in the Intelligence Community by up to 10% should there be a determination that activities performed by a contractor should be done by a U.S. government employee."
The problem is two-fold. Part of the problem, according to Author Tim Weiner, is that political appointees designated by recent presidential administrations have sometimes been under-qualified or over-zealous politically. Large scale purges have taken place in the upper echelons of the CIA, and when those talented individuals are pushed out the door they have frequently gone on to found new independent intelligence companies which can suck up CIA talent. Another part of the contracting problem comes from Congressional restrictions on the number of employees within the IC. According to Hillhouse, this resulted in 70% of the de facto workforce of the CIA's National Clandestine Service being made up of contractors. "After years of contributing to the increasing reliance upon contractors, Congress is now providing a framework for the conversion of contractors into federal government employees – more or less." The number of independent contractors hired by the Federal government across the intelligence community has skyrocketed. So, not only does the CIA have trouble hiring, but those hires will frequently leave their permanent employ for shorter term contract gigs which have much higher pay and allow for more career mobility.
As with most government agencies, building equipment often is contracted. The National Reconnaissance Office (NRO), responsible for the development and operation of airborne and spaceborne sensors, long was a joint operation of the CIA and the United States Department of Defense. The NRO had been significantly involved in the design of such sensors, but the NRO, then under DCI authority, contracted more of the design that had been their tradition, and to a contractor without extensive reconnaissance experience, Boeing. The next-generation satellite Future Imagery Architecture project "how does heaven look," which missed objectives after $4 billion in cost overruns, was the result of this contract.
Some of the cost problems associated with intelligence come from one agency, or even a group within an agency, not accepting the compartmented security practices for individual projects, requiring expensive duplication.
In fiction
Fictional depictions of the CIA exist in many books, films and video games. Some fiction draws, at least in parts, on actual historical events, while other works are entirely fictional. The television series Chuck (2007), was based solely on a man who accidentally sees secret CIA encryptions and eventually becomes an asset/liability, and later on an agent in the agency. Films include Charlie Wilson's War (2007), based on the story of U.S. Congressman Charlie Wilson and CIA operative Gust Avrakotos, who supported the Afghan mujahideen, and The Good Shepherd (2006), a fictional spy film produced and directed by Robert De Niro based loosely on the development of counter-intelligence in the CIA. The fictional character Jack Ryan in Tom Clancy's books is a CIA analyst. Graham Greene's The Quiet American is about a CIA agent operating in Southeast Asia. Fictional depictions of the CIA are also used in video games, such as Tom Clancy's Splinter Cell, Call of Duty: Modern Warfare 2 and Call of Duty: Black Ops.